 Wouldn't you love to replace password based access control to avoid having to reset forgotten password and worry about the intergrity of your system? Wouldn’t you like to rest secure in comfort that your healthcare system does not merely on your social security number as proof of your identity for granting access to your medical records?
Wouldn't you love to replace password based access control to avoid having to reset forgotten password and worry about the intergrity of your system? Wouldn’t you like to rest secure in comfort that your healthcare system does not merely on your social security number as proof of your identity for granting access to your medical records? Because each of these questions is becoming more and more important, access to a reliable personal identification is becoming increasingly essential .Conventional method of identification based on possession of ID cards or exclusive knowledge like a social security number or a password are not all together reliable. ID cards can be lost forged or misplaced; passwords can be forgotten or compromised. But a face is undeniably connected to its owner. It cannot be borrowed stolen or easily forged
The information age is quickly revolutionizing the way transactions are completed. Everyday actions are increasingly being handled electronically, instead of with pencil and paper or face to face. This growth in electronic transactions has resulted in a greater demand for fast and accurate user identification and authentication. Access codes for buildings, banks accounts and computer systems often use PIN's for identification and security clearences.
Using the proper PIN gains access, but the user of the PIN is not verified. When credit and ATM cards are lost or stolen, an unauthorized user can often come up with the correct personal codes. Despite warning, many people continue to choose easily guessed PIN's and passwords: birthdays, phone numbers and social security numbers. Recent cases of identity theft have hightened the nee for methods to prove that someone is truly who he/she claims to be.
Face recognition technology may solve this problem since a face is undeniably connected to its owner expect in the case of identical twins. Its nontransferable. The system can then compare scans to records stored in a central or local database or even on a smart card.
What are biometrics?
A biometric is a unique, measurable characteristic of a human being that can be used to automatically recognize an individual or verify an individual’s identity. Biometrics can measure both physiological and behavioral characteristics. Physiological biometrics (based on measurements and data derived from direct measurement of a part of the human body) include:
· Finger-scan
· Facial Recognition
· Iris-scan
· Retina-scan
· Hand-scan
Behavioral biometrics (based on measurements and data derived from an action) include:
· Voice-scan
· Signature-scan
· Keystroke-scan
A “biometric system” refers to the integrated hardware and software used to conduct biometric identification or verification.
Why we choose face recognition over other biometric?
There are a number reasons to choose face recognition. This includes the following
1. It requires no physical inetraction on behalf of the user.
2. It is accurate and allows for high enrolment and verification rates.
3. It does not require an expert to interpret the comparison result.
4. It can use your existing hardware infrastructure, existing camaras and image capture devices will work with no problems.
5. It is the only biometric that allow you to perform passive identification in a one to many environment (eg: identifying a terrorist in a busy Airport terminal.
FACE RECOGNITION
THE FACE:
The face is an important part of who you are and how people identify you. Except in the case of identical twins, the face is arguably a person's most unique physical characteristics. While humans have the innate ability to recognize and distinguish different faces for millions of years , computers are just now catching up.
For face recognition there are two types of comparisons .the first is verification. This is where the system compares the given individual with who that individual says they are and gives a yes or no decision. The second is identification. This is where the system compares the given individual to all the
other individuals in the database and gives a ranked list of matches. All identification or authentication technologies operate using the following four stages:
other individuals in the database and gives a ranked list of matches. All identification or authentication technologies operate using the following four stages:
· capture: a physical or behavioural sample is captured by the system during enrollment and also in identification or verification process.
· Extraction: unique data is extracted from the sample and a template is created.
· Comparison: the template is then compared with a new sample.
· Match/non match : the system decides if the features extracted from the new sample are a match or a non match.
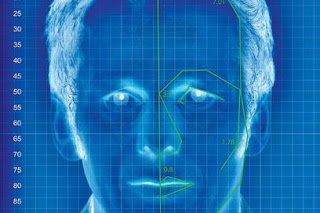
Face recognition technology analyze the unique shape ,pattern and positioning of the facial features. Face recognition is very complex technology and is largely software based. This Biometric Methodology establishes the analysis framework with tailored algorithms for each type of biometric device. Face recognition starts with a picture, attempting to find a person in the image. This can be accomplished using several methods including movement, skin tones, or blurred human shapes. The face recognition system locates the head and finally the eyes of the individual. A matrix is then developed based on the characteristics of the individual’s face. The method of defining the matrix varies according to the algorithm (the mathematical process used by the computer to perform the comparison). This matrix is then compared to matrices that are in a database and a similarity score is generated for each comparison.
Artificial intelligence is used to simulate human interpretation of faces. In order to increase the accuracy and adaptability , some kind of machine learning has to be implemented.
There are essentially two methods of capture. One is video imaging and the other is thermal imaging. Video imaging is more common as standard video cameras can be used. The precise position and the angle of the head and the surrounding lighting conditions may affect the system performance. The complete facial image is usually captured and a number of points on the face can then be mapped, position of the eyes, mouth and the nostrils as a example. More advanced technologies make 3-D map of the face which multiplies the possible measurements that can be made. Thermal imaging has better accuracy as it uses facial temperature variations caused by vein structure as the distinguishing traits. As the heat pattern is emitted from the face itself without source of external radiation these systems can capture images despite the lighting condition, even in the dark. The drawback is high cost. They are more expensive than standard video cameras.
CAPTURING OF IMAGE BY STANDARD VIDEO CAMERAS
The image is optical in characteristics and may be thought of as a collection of a large number of bright and dark areas representing the picture details. At an instant there will be large number of picture details existing simultaneously each representing the level of brightness of the scene to be reproduced. In other words the picture information is a function of two variables: time and space. Therefore it would require infinite number of channels to transmit optical information corresponding to picture elements simultaneously. There are practical difficulty in transmitting all information simultaneously so we use a method called scanning.
Here the conversion of optical information to electrical form and its transmission is carried out element by element one at a time in a sequential manner to cover the entire image. A TV camera converts optical information into electrical information, the amplitude of which varies in accordance with variation of brightness.
An optical image of the scene to be transmitted is focused by lense assembly on the rectangular glass plate of the camera tube. The inner side of this has a transparent coating on which is laid a very thin layer of photoconductive material. The photolayer has very high resistance when no light is falling on it but decreases depending on the intensity of light falling on it. An electron beam is formed by an electron gun in the TV camera tube. This beam is used to pick up the picture information now avilable on the target plate of varying resistace at each point.
The electron beam is deflected by a pair of deflecting coils mounted on the glass envelope and kept mutually perpendicular to each other to achive scanning of the entire target area. The deflecting coils are fed seperately from two sweep oscillators, each operating at different frequencies. The magnetic deflection caused by current in one coil gives horizontal motion to the beam from left to right at a uniform rate and brings it back to the left side to commence the trace of the next line. The other coil is used to deflect the beam from top to bottom.
As the beam moves from element to element it encounters different resistance across the target plate depending on the resistance of the photoconductive coating. The result is flow of current which varies in magnitude as elements are scanned. The current passes through the load resistance Rl connected to conductive coating on one side of the DC supply source on the other. Depending on the magnitude of current a varying voltage appears across the resistance Rl and this corresponds to the optical information of the picture
COMPONENTS OF FACE RECOGNITION SYSTEMS
· An automated mechanism that scans and captures a digital or an analog image of a living personal characteristics.(enrollment module)
· Another entity which handles compression, processing, storage and compression of the captured data with stored data (database)
· The third interfaces with the application system ( identification module)
User interface captures the analog or digital image of the person's face. In the enrollment module the obtained sample is preprocessed and analyzed. This analyzed data is stored in the database for the purpose of future comparison.
The database compresses the obtained sample and stores it. It should have retrival property also that is it compares all the stored sample with the newly obtained sample and retrives the matched sample for the purpose of verification by the user and determine whether the match declared is right or wrong.
The verification module also consists of a preprocessing system. Verification means the system checks as to who the person says he or she is and gives a yes or no decision. In this module the newly obtained sample is preprocessed and compared with the sample stored in the database. The decision is taken depending on the match obtained from the database. Correspondingly the sample is accepted or rejected.
Instead of verification module we can make use of identification module. In this the sample is compared with all the other samples stored in the database. For each comparison made a match score is given. The decision to accept or reject the sample depends on this match score falling above or below a predetermined threshold.
CONCLUSION
Face recognition technologies have been associated generally with very costly top secure applications. Today the core technologies have evolved and the cost of equipments is going down dramatically due to the intergration and the increasing processing power. Certain application of face recognition technology are now cost effective, reliable and highly accurate. As a result there are no technological or financial barriers for stepping from the pilot project to widespread deployment.
No comments:
Post a Comment
leave your opinion